Revealed: How a Deepfake Hack Caused the Massive UXLINK Exploit, Not a Rug Pull

BitcoinWorld
Revealed: How a Deepfake Hack Caused the Massive UXLINK Exploit, Not a Rug Pull
The crypto community was shaken in September when news broke of a multi-million dollar exploit on UXLINK. Immediate whispers of an ‘inside job’ or rug pull spread like wildfire. However, the platform’s team has now presented compelling evidence pointing to a far more sinister and sophisticated cause: a deepfake-enabled external hack. This revelation shifts the narrative from potential malpractice to a stark warning about next-generation digital threats in Web3.
What Really Caused the UXLINK Hack?
According to a detailed statement from CEO RollandSaf, the September 22nd incident, which led to the loss of approximately $11 million in assets, was the result of a meticulously planned external attack. The hacker did not brute-force the system’s code. Instead, they employed social engineering tactics of alarming sophistication.
The attacker posed as a legitimate business partner. Using deepfake technology, they conducted convincing video conferences to gain the trust of a UXLINK team member. This elaborate ruse was the key that unlocked access to the team member’s Telegram account and personal device.
How Did the Attacker Exploit the UXLINK System?
With this unauthorized access, the hacker’s actions were swift and devastating. They seized control of a critical smart contract. This control allowed them to perform an illegal function: minting billions of arb-UXLINK tokens out of thin air.
- Supply Inflation: The total token supply was artificially inflated to over 10.006 trillion.
- Funds Access: The breach also provided unauthorized access to the project’s treasury and ecosystem funds.
- Immediate Fallout: The event triggered panic, with many fearing a classic ‘rug pull’ where developers abandon a project after stealing funds.
UXLINK’s Crisis Response and User Compensation
Facing the crisis while attending Korea Blockchain Week (KBW), the UXLINK team initiated a global response. They immediately coordinated with major cryptocurrency exchanges to freeze suspicious transactions. Furthermore, they engaged top security firms for forensic analysis and alerted multinational law enforcement agencies.
The recovery process was multi-faceted and user-focused:
- Contract Rebuild: The compromised smart contract was completely scrapped and rebuilt from the ground up.
- Token Restoration: 479 million circulating UXLINK tokens were restored on a strict one-to-one basis for legitimate holders.
- Community Governance: A governance vote was held, resulting in the early unlock of 12% of tokens specifically to compensate affected users.
- Buyback Initiative: Some of the recovered assets were used for a token buyback to help stabilize the ecosystem.
Why This UXLINK Incident Is a Warning for Web3
This exploit transcends a simple smart contract bug. It highlights a critical vulnerability in the human layer of blockchain security. Deepfake technology is becoming increasingly accessible, making video and audio impersonation a potent tool for hackers. This UXLINK hack serves as a case study for all Web3 projects: security must encompass not just code audits, but also team training on advanced social engineering threats.
CEO RollandSaf strongly refuted the rug pull allegations, emphasizing that UXLINK is a project with real revenue streams and a substantial global user base. The team’s transparent, active response—rebuilding, compensating, and cooperating with authorities—stands in contrast to the behavior typically seen in exit scams.
Conclusion: Resilience in the Face of Sophisticated Attacks
The UXLINK hack story is ultimately one of resilience. It demonstrates how a decentralized project can confront a severe crisis with transparency and user-centric action. While the financial loss was significant, the platform’s swift response to the external hack, its commitment to making users whole, and its public detailing of the deepfake methodology provide a valuable lesson for the entire industry. The future of Web3 depends not only on immutable code but also on educated, vigilant communities and teams prepared for evolving digital deceptions.
Frequently Asked Questions (FAQs)
Was the UXLINK incident a rug pull?
No. According to the official investigation, the event was an external hack using deepfake technology to trick a team member, not an exit scam by the developers.
How much was stolen in the UXLINK hack?
Approximately $11 million in assets was compromised during the exploit on September 22nd.
What is a deepfake hack?
A deepfake hack uses artificial intelligence to create convincing fake video or audio of a person. In this case, the hacker impersonated a business partner to gain trust and access.
How did UXLINK compensate its users?
Through a community governance vote, 12% of tokens were unlocked early to compensate affected users. The team also restored all legitimate tokens on a 1:1 basis after rebuilding the smart contract.
What has UXLINK done to prevent future hacks?
UXLINK has rebuilt its smart contract system, enhanced internal security protocols, and is emphasizing training for team members on identifying advanced social engineering attacks like deepfakes.
Are user funds now safe on UXLINK?
The platform has restored its system with a new, audited smart contract and implemented stricter security measures. However, as with any crypto project, users should always practice personal security diligence.
Found this deep dive into the UXLINK hack insightful? The world of Web3 security is constantly evolving. Help others stay informed by sharing this article on your social media channels. Discussing these incidents openly makes the entire ecosystem stronger and safer for everyone.
To learn more about the latest trends in blockchain security and exploits, explore our article on key developments shaping DeFi protocols and institutional adoption of crypto asset protection standards.
This post Revealed: How a Deepfake Hack Caused the Massive UXLINK Exploit, Not a Rug Pull first appeared on BitcoinWorld.
You May Also Like
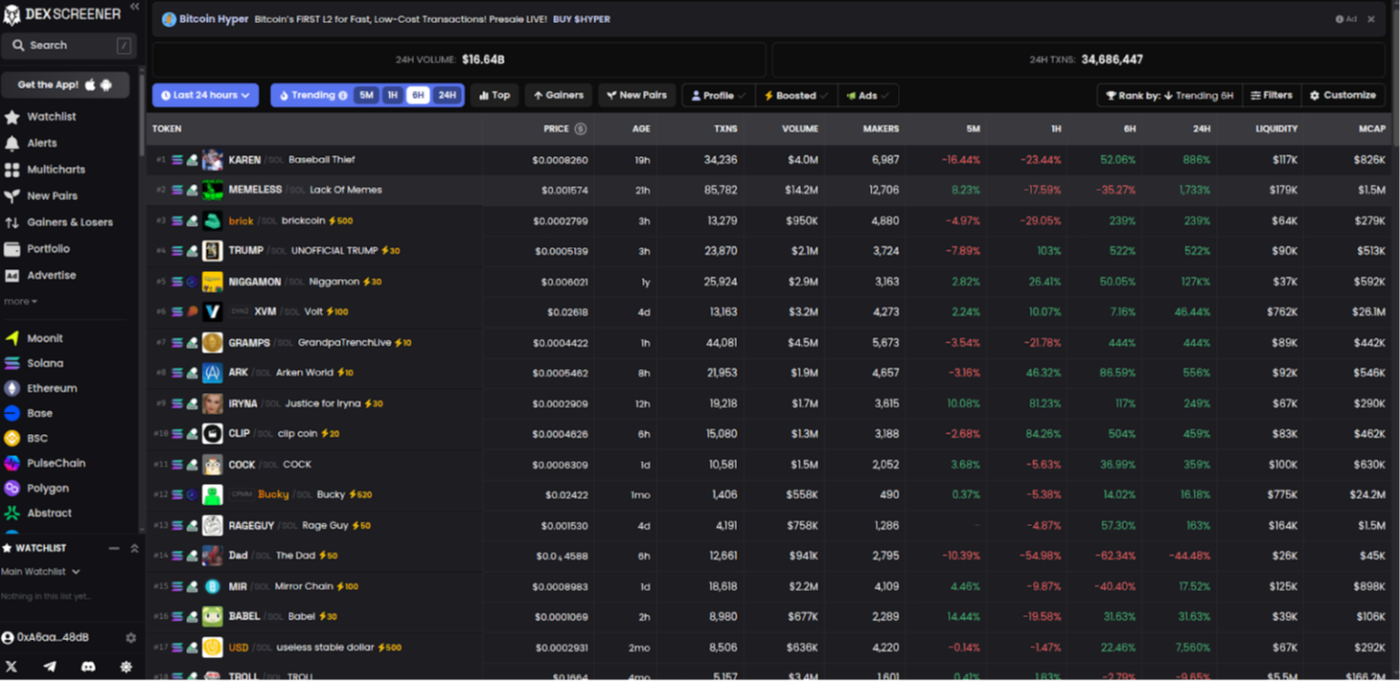
Building a DEXScreener Clone: A Step-by-Step Guide
Which DOGE? Musk's Cryptic Post Explodes Confusion
